Industrial Cyber Security Solutions and Services Market Outlook:
Industrial Cyber Security Solutions and Services Market size was valued at USD 22.15 billion in 2025 and is set to exceed USD 56.93 billion by 2035, expanding at over 9.9% CAGR during the forecast period i.e., between 2026-2035. In the year 2026, the industry size of industrial cyber security solutions and services is evaluated at USD 24.12 billion.
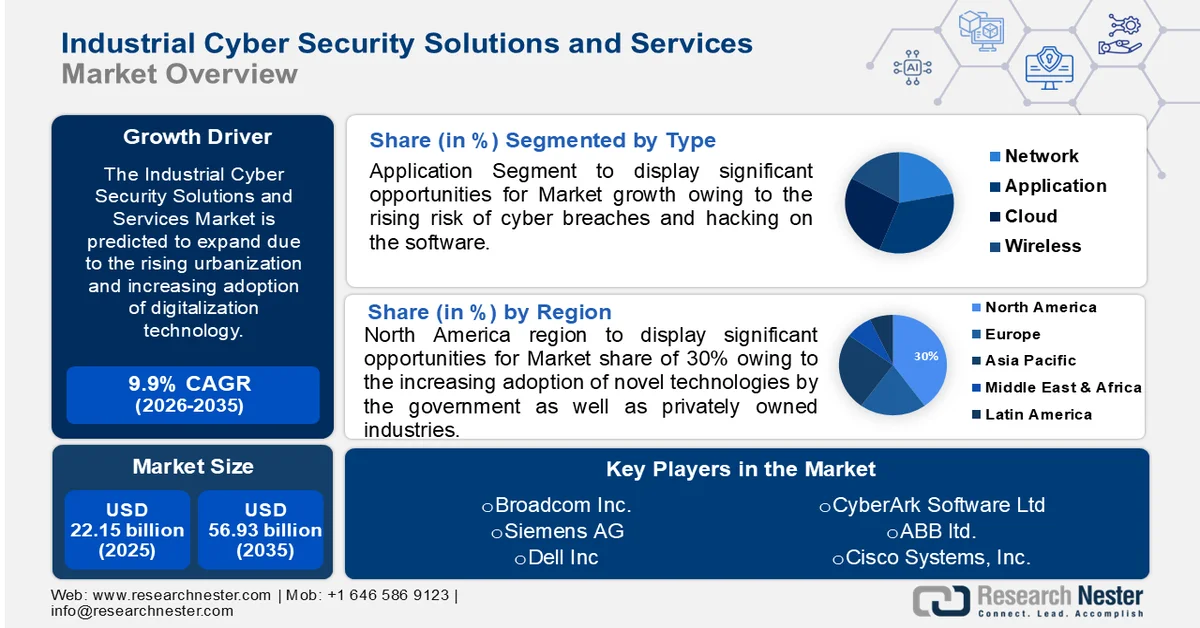
The growth of the market can be attributed to the rising urbanization and increasing adoption of digitalization technology across the world. The growing use of different technologies including cloud computing, AI, and other applications is estimated to drive market growth. Also, the rising number of cyber-attacks or cybercrimes in many IT and data centers is driving market growth in the coming years. As per the reports, it was estimated that every 30 seconds a cyber-attack is carried out online with cybercrimes occurring more than 2400 times every day around the world. The growing number of industries using advanced technological data management services to reduce the workload is estimated to drive market growth in the coming years.
Key Industrial Cyber Security Solutions and Services Market Insights Summary:
Regional Highlights:
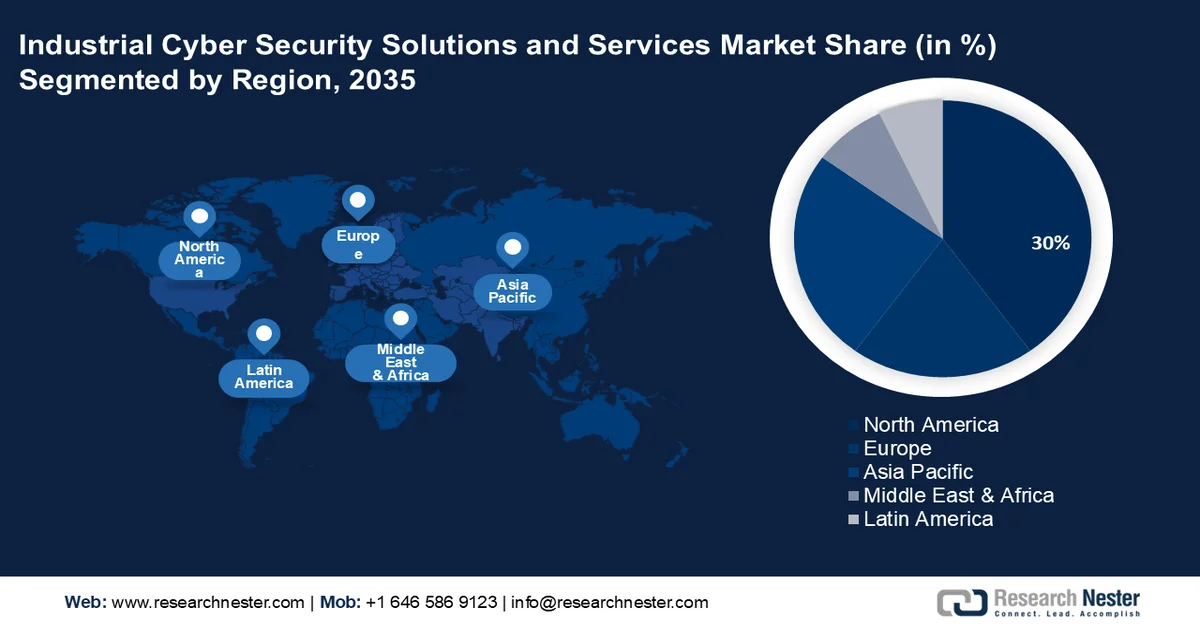
- North America is projected to account for 30% revenue share of the industrial cyber security solutions and services market by 2035, driven by escalating government IT spending, expanding IoT adoption, and increased deployment of cloud security solutions across industries.
- Asia Pacific is anticipated to witness notable growth by 2035, fueled by rising investments in technological advancements and the growing economic losses from escalating cybercrimes.
Segment Insights:
- In the industrial cyber security solutions and services market, the application segment is projected to secure the largest share by 2035, driven by the escalating incidence of software hacking and cyber breaches across industrial systems.
- The transportation segment is expected to capture a significant share by 2035, owing to the growing reliance on online travel applications and the heightened risk of personal data exposure.
Key Growth Trends:
- Increasing Incidences of Industrial Cybercrimes Owing to Security Breaches
- Growing Adoption of Cyber Security Services with Increasing Cyberattacks
Major Challenges:
- Lack of Awareness About the Cruciality of Cybersecurity
- Require Regular Updating of the Systems to Remain Up to Date
Key Players: Intel Corporation, Freescale Semiconductor Inc., GCT Semiconductor Inc., GainSpan Corporation, Broadcom Corporation, Atmel Corporation, Greenpeak Technologies Ltd., Altair Semiconductor, Inc., Ammimon Ltd., Texas Instruments, Inc.
Global Industrial Cyber Security Solutions and Services Market Forecast and Regional Outlook:
Market Size & Growth Projections:
- 2025 Market Size: USD 22.15 billion
- 2026 Market Size: USD 24.12 billion
- Projected Market Size: USD 56.93 billion by 2035
- Growth Forecasts: 9.9% CAGR (2026-2035)
Key Regional Dynamics:
- Largest Region: North America (30% Share by 2035)
- Fastest Growing Region: Asia Pacific
- Dominating Countries: United States, Israel, Germany, United Kingdom, Japan
- Emerging Countries: China, India, Brazil, Mexico, Israel
Last updated on : 25 February, 2026
Industrial Cyber Security Solutions and Services Market - Growth Drivers and Challenges
Growth Drivers
-
Increasing Incidences of Industrial Cybercrimes Owing to Security Breaches – Cybercrimes are increasing in the IT and industrial sectors to collect all informational data and use that for their personal benefit or sell them to people needed. This leads to the loss of properties, and the financial, and personal activity of the business owners. Cyberattacks are carried out through networked devices, computers, or laptops hence cybersecurity is required to protect the unwanted entry into the system. All these incidents are driving market growth in the coming years. The number of websites that get hacked every day across the world was estimated to be over 28,000.
-
Growing Adoption of Cyber Security Services with Increasing Cyberattacks – The value of cybersecurity around the world in the year 2022 was estimated to be over USD 200 billion.
-
Increasing Automotive Industries across the World Owing to Increasing Need for Personal Vehicles – The increasing use of AI in automotive vehicles can exchange data with surrounding vehicles and other multiple parties such as surrounding infrastructure and any IoT device which allows hackers. This is expected to generate new threats and vulnerabilities to the ecosystem, and access to intellectual property, leading to faulty behavior, and shutdown of systems. The global automotive manufacturing sector produced a revenue worth about USD 3 trillion in the year 2021 according to estimations.
-
Rising Number of Oil and Gas Extractions with Growing Need – The oil and gas sectors are the major target of nation-state actors, hacktivists, and various attackers with economic, political, and strategic interests. The high dependency on technology and information control systems is expected to create serious outcomes which include operational disruptions, environmental harm, reputation damage, and huge economic loss. As per the reports, in the U.S. the oil and gas extraction sectors’ gross output reached USD 40 billion in the year 2021.
Challenges
- Lack of Awareness About the Cruciality of Cybersecurity
- Require Regular Updating of the Systems to Remain Up to Date - The business organization should regularly update the software, and hardware of the systems and other control devices to prevent any threat and should always maintain a security strategy and monitor the activity of attackers a step ahead. All these require skills, and experienced personnel may increase the cost and time of management which is estimated to hamper the market growth.
- Need for Complex Setup and Security Architectures and Tools
Industrial Cyber Security Solutions and Services Market Size and Forecast:
| Report Attribute | Details |
|---|---|
|
Base Year |
2025 |
|
Forecast Year |
2026-2035 |
|
CAGR |
9.9% |
|
Base Year Market Size (2025) |
USD 22.15 billion |
|
Forecast Year Market Size (2035) |
USD 56.93 billion |
|
Regional Scope |
|
Industrial Cyber Security Solutions and Services Market Segmentation:
Type Segment Analysis
The global industrial cyber security solutions and services market is segmented and analyzed for demand and supply by type into the network, application, cloud, wireless, and others. Out of these types, the application segment is estimated to gain the largest market share over the projected time frame. Application security is a security system that protects the software of industries from cybercrimes, data breaches, and other threats. The rising risk of cyber breaches and hacking on the software is estimated to drive market growth. It was reported that globally more than 44% of cyber breaches are included in hacking and over 20% are included as errors or casual events. The application security system includes firewalls, data encryption, and antivirus systems that cease the entry of unauthorized users into the systems. The security application includes the safety of external and internal software and coding threats that involve various web attacks, DDoS attacks, fraud, and site scraping. Also, the security application policies help to protect all industrial applications, websites, and sensitive data from random security attacks.
End-user Segment Analysis
The global industrial cyber security solutions and services market is also segmented and analyzed for demand and supply by end-user into utilities, transportation, chemicals & manufacturing, and others. Amongst these segments, the transportation segment is expected to garner a significant share. The transportation segment growth is attributed to the increasing number of people using web applications for travel tickets. Approximately more than 1 billion population worldwide used travel applications as of 2019. Also, the rising risk of exposure to personal details and other information is estimated to hike the market growth in the coming years. All the transport services such as railways, roads, cabs, and metros, are providing online services to the public to reduce waiting time and improve customer satisfaction. Online travel booking service has a passenger information system that may lead to hacking of all the personal details. All these factors increase the utilization of internet and web applications thereby increasing the risk of cyber-attacks which in turn boosts the market growth.
Our in-depth analysis of the global market includes the following segments:
|
By Type |
|
|
By Offering |
|
|
By End-User Industry |
|

Vishnu Nair
Head - Global Business DevelopmentCustomize this report to your requirements — connect with our consultant for personalized insights and options.
Industrial Cyber Security Solutions and Services Market - Regional Analysis
North American Market Insights
North America industry is poised to dominate majority revenue share of 30% by 2035, The market in North America region is estimated to garner the largest share over the forecast period on the back of the increasing adoption of novel technologies by the government as well as privately owned industries. The government IT expenditure in the U.S. crossed USD 86 billion in 2019, which was projected to cross USD 92 billion by the end of 2021. The increasing population using the internet across the world with the growing utilization of smartphones, computers, and laptops is estimated to drive the market growth in the region. Also, the rising adoption of IoT in organizations to manage and regulate industrial control systems security and the increasing application of cloud security solutions to enhance security is anticipated to hike the market growth in the coming years.
APAC Market Insights
The market in the Asia Pacific region is estimated to witness modest growth over the forecast period, owing to the increasing investment in technological development in the countries, such as India, Japan, and China. Moreover, the emergence of new industries and up-surge in the cybercrimes are estimated to boost the market growth. According to the estimations, a loss of more than USD 1 trillion was reported in the Asia Pacific region owing to cybercrime every year.
Industrial Cyber Security Solutions and Services Market Players:
- Honeywell International Inc.
- Company Overview
- Business Strategy
- Key Product Offerings
- Financial Performance
- Key Performance Indicators
- Risk Analysis
- Recent Development
- Regional Presence
- SWOT Analysis
- Broadcom Inc.
- International Business Machines Corporation
- Cisco Systems, Inc.
- ABB Ltd.
- Schneider Electric SE
- CyberArk Software Ltd.
- Dell Inc.
- Siemens AG
- Maverick Technologies
Recent Developments
-
Honeywell International Inc. declared the launch of a new operational technology cybersecurity solution to support its customers in protecting the availability, safety, and reliability of industrial control operations and systems.
-
International Business Machines Corporation and ABB ltd. declared a merging of both focused on combing cybersecurity and operational technology.
- Report ID: 3659
- Published Date: Feb 25, 2026
- Report Format: PDF, PPT
- Explore a preview of key market trends and insights
- Review sample data tables and segment breakdowns
- Experience the quality of our visual data representations
- Evaluate our report structure and research methodology
- Get a glimpse of competitive landscape analysis
- Understand how regional forecasts are presented
- Assess the depth of company profiling and benchmarking
- Preview how actionable insights can support your strategy
Explore real data and analysis
Frequently Asked Questions (FAQ)
Industrial Cyber Security Solutions and Services Market Report Scope
Free Sample includes current and historical market size, growth trends, regional charts & tables, company profiles, segment-wise forecasts, and more.
Connect with our Expert
Copyright @ 2026 Research Nester. All Rights Reserved.




